HelloID Access Management is a cloud-based module that plays a key role in the Identity and Access Management (IAM) solution, HelloID. The module provides employees with simple, fast, and user-friendly access to all the business applications they use. This raises productivity, ensures optimal security, and improves user satisfaction.
Does logging in to IT services take your employees a lot of time?
Do employees frequently get blocked because they forgot their password?
Is your helpdesk under pressure from the volume of forgotten password tickets?
These challenges are now a thing of the past!
One Login, Full Access: Work Securely and Efficiently with HelloID
Your employees work across various applications. For security, each application requires unique credentials, which means users quickly have to remember dozens of logins. This introduces challenges. Employees may forget their passwords, leading to lost productivity. They may also choose weaker passwords so they are easier to remember. This directly affects your organization’s security.
High productivity requires optimal access to the applications employees need. HelloID Access Management delivers this with precision. With HelloID, employees log in once to a user-friendly dashboard that grants access to all their cloud applications from any location and any device.
Capabilities with Access Management
Support For a Broad Range of Applications
Employees rely on a wide range of IT applications to perform daily work. HelloID Access Management supports all your cloud-based IT systems and applications. This optimizes access across your entire IT landscape.
A User-Friendly Digital Workspace
HelloID Access Management integrates seamlessly with the portals of leading social intranet and IT management solutions, including TOPdesk, AFAS, SharePoint, Embrace, triptic (Iris Intranet), and a&m impact. Users sign in to the social intranet and gain access to their personal portal. This portal provides all the information and communication tools they need. The HelloID widget gives them direct access to business applications from within the social intranet. This creates a user-friendly digital workspace for your professionals.

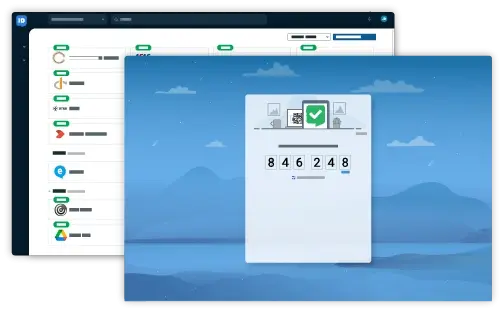
Additional Security with MFA
Each application requires a different level of security. For your most sensitive applications, you may want to enforce multifactor authentication (MFA). Employees then sign in with a username and password and must complete one or more additional verifications. HelloID Access Management provides broad support for this, including several free methods such as FIDO, Push-to-Verify, SMS, and email. The module also integrates seamlessly with Microsoft Authenticator and Google Authenticator, and it can continue to support MFA methods and tokens you already use.

A Unified Authentication Method
Driven by ISO and NEN guidelines, more software vendors are requiring MFA. In practice, this results in a proliferation of authentication methods. HelloID Access Management puts an end to this by consolidating MFA into a single, unified method. This increases usability.
HelloID Modules and Pricing
Calculate the price based on the
number of users per month.
per month