HelloID Modules
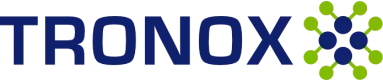
User Provisioning
HelloID Provisioning establishes a connection between the HR system and user accounts in the network. The module automates the full joiner, mover, and leaver process and processes changes quickly, accurately, and efficiently.
User Provisioning & Lifecycle Management
Automate and simplify the management of user accounts throughout their entire lifecycle with HelloID’s User Provisioning and Lifecycle Management. Create, modify, and enable or disable accounts seamlessly, which minimizes errors and improves productivity.
Role Based Access Control
Optimize your organization’s security and compliance with HelloID’s Role-Based Access Control (RBAC). Assign entitlements based on roles, simplify the authorization model, and reduce the risk of unauthorized access.
Service Automation
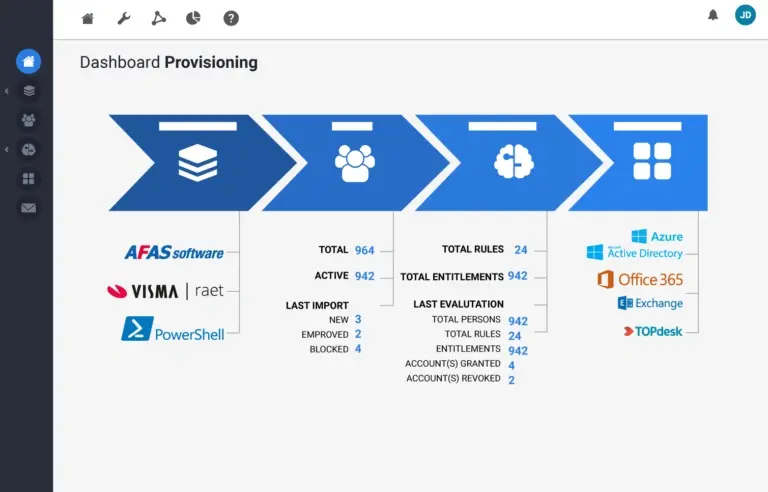
HelloID supports your IT department with the Service Automation module. End users can request access to applications or data online themselves. Their manager can approve with one click, after which the module automatically applies the change across the IT infrastructure.
Self-Service & Workflow Management
Discover the power of Self-Service and Workflow Management in HelloID Service Automation. Users can easily manage IT requests through an intuitive catalog, while automated workflows accelerate approvals and ensure compliance.
Helpdesk Delegation
Optimize IT support with HelloID’s Helpdesk Delegation feature. Assign specific tasks to authorized service desk staff without granting full access, which improves security and increases efficiency.
Access Management
HelloID Access Management provides employees, partners, and optionally customers with simple and consistent access to cloud applications. Authentication is handled through a username and password. You can enable two-factor authentication for additional verification.
Single Sign-On
With HelloID Access Management we provide Single Sign-On (SSO) for seamless and secure access to multiple applications with a single login. Increase productivity and strengthen your security because employees no longer need to remember multiple passwords.
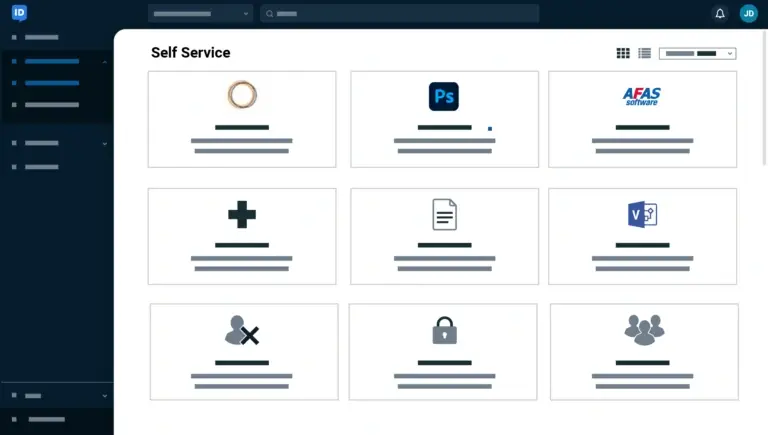
Multi-Factor Authentication
Add an extra layer of security with HelloID’s Multi-Factor Authentication (MFA). Verify users through multiple methods and protect data against unauthorized access, even if passwords are compromised.
Governance
HelloID Governance extends the capabilities of Provisioning and Service Automation with advanced tools that provide continuous insight into policy compliance and make it easier to detect anomalies. This new module, available starting in 2025, supports organizations in a time when compliance and security are central.
Provisioning
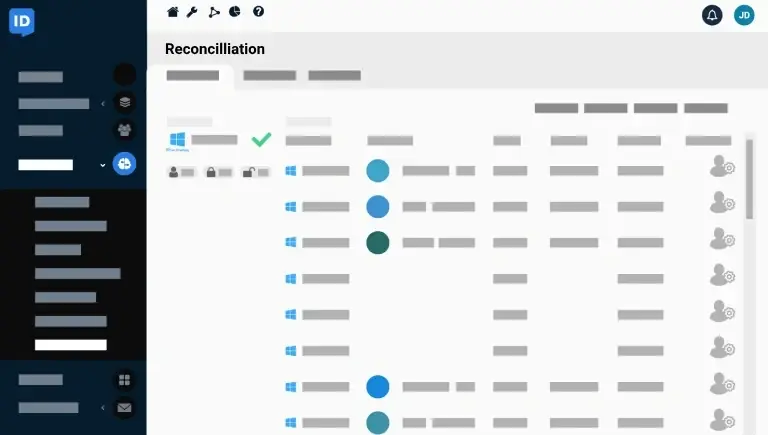
HelloID Governance strengthens Provisioning with Reconciliation, which quickly identifies deviations and orphaned accounts. Using pattern recognition, you receive recommendations for authorization models that fit your organization. Segregation of Duties ensures that conflicting entitlements are avoided.
Service Automation
HelloID Governance extends Service Automation with periodic recertification to keep self-service products up to date. AI-driven recommendations help optimize your authorization processes, while advanced workflows enable new options such as involving site managers in approvals.
HelloID modules and pricing
Calculate the price based on the
number of users per month.
per month
Featured
Connectors
HelloID integrates with a wide range of applications and systems that you can use as source or target systems. Explore the unmatched catalog of connectors for your applications. Simplify administration and integration with automated user management and streamlined access control.
IAM in the Cloud
HelloID delivers IAM from the cloud. You do not need to invest in your own infrastructure with hardware, storage, security, and identity management software. Installation and configuration literally take hours, and Tools4ever manages the solution, including automatic updates.
You only need to take care of organization-specific items yourself, and that is very simple with HelloID. Lower costs and minimal administration do not come at the expense of control and security. On the contrary, Tools4ever’s Identity as a Service (IDaaS) runs on a highly secured infrastructure, which is thoroughly assessed every six months by an independent party every six months. Compliance with stringent security requirements is therefore assured.