
Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC) is a method for managing authorization within your organization. You do not assign authorizations on an individual basis; instead, you assign them by role. These roles are derived from an employee's department, job function, location, and cost center within your organization. In this article, you will learn everything about RBAC, RBAC roles, and granting permissions based on these roles.
Within Identity and Access Management (IAM), RBAC can play an important role. By assigning permissions via RBAC, you can define the permissions that specific user groups receive in a single pass. This saves significant time, eliminates the need to grant authorizations to individual users, and reduces human error. The various RBAC roles are generally documented in an RBAC table.
RBAC Model
A key advantage of RBAC is the use of RBAC roles. These allow you to define all required permissions for a specific user group in a single step. For example, consider an employee who works on your organization’s finance team. To perform their job, this employee needs access to the CRM, ERP, and order systems, as well as various other data sources. With RBAC, you configure it so that every employee active in your finance department automatically receives the required permissions.
This approach saves considerable time. You do not need to assign permissions to individual users, and you can be confident that all users have the permissions required to perform their jobs. The reverse also applies. If a finance employee leaves for another company or receives a different role within your organization, RBAC automatically adjusts the user’s authorizations to the new job function.
In an IAM solution such as HelloID, you define these authorizations in business rules. This is useful because once configured, the RBAC process is fully automated. The IAM solution assigns permissions based on your business rules and each user's role. Want to know exactly how this works? Then view our RBAC page.
The Advantages and Disadvantages of RBAC
RBAC offers many advantages, but it also has several considerations.
Advantages
Simplify Access Permissions: With RBAC, you can significantly streamline access management. You assign permissions based on roles instead of individual users. This not only saves time but also reduces the likelihood of human error.
Compliance with Laws and Regulations: RBAC enables you to arrange authorizations in a structured, standardized, and transparent way. This is important for regulatory compliance, such as the General Data Protection Regulation (GDPR). RBAC makes it straightforward to demonstrate that sensitive data is only visible to authorized employees.
Disadvantages
Complexity: Implementing RBAC can be relatively complex. You must define all roles in your organization and their associated responsibilities before you can begin RBAC. You can simplify this process with role mining, a technique that analyzes employees’ existing authorizations to derive roles.
Role Explosion: You may encounter a role explosion, where the number of roles in your organization increases rapidly. The risk is that administration shifts from individual users to an uncontrolled proliferation of roles. The administrative burden shifts rather than decreases. We therefore recommend using service automation to assign temporary permissions and similar access to users.
RBAC vs ABAC
A method that closely resembles RBAC is Attribute-Based Access Control (ABAC). The main difference between the two methods is how authorizations are assigned. With RBAC, you assign authorizations based on roles. These roles are based on department, location, job level, and work-related tasks.
With ABAC, you assign authorizations based on user and object attributes and the types of actions performed. For example, you can assign permissions based on the user, specifically looking at job title, typical tasks, or job level to determine the type of work a user performs. Also consider the attributes of the objects users are trying to access. This can include the file type, the creator, or the file's sensitivity. The time a user attempts to access a file, such as the date and time, can also be decisive in ABAC when granting permissions.
RBAC and ABAC in Practice
A concrete example is a healthcare organization that wants to grant physicians access to patient records. If you use RBAC, you can grant access to all patient records based on a physician's role. You can also grant location-based access to all patient records linked to that location. In this case, you largely rely on static data.
If you use ABAC, you can apply multiple attributes that can be dynamic. For example, you can grant physicians access to patient records for patients with whom they have a direct physician-patient relationship, as defined by the scheduling system. ABAC, therefore, enables more precise tailoring of authorizations to users' actual needs and offers greater flexibility than RBAC.
Role Engineering: Top-Down or Bottom-Up
Want to get started with RBAC? Then begin by defining the roles present within your organization. You can choose between two approaches: top-down and bottom-up. With a top-down approach, you start the process from your organization's job functions, whereas a bottom-up approach starts with user data. Both approaches have their own advantages. Below are the differences.
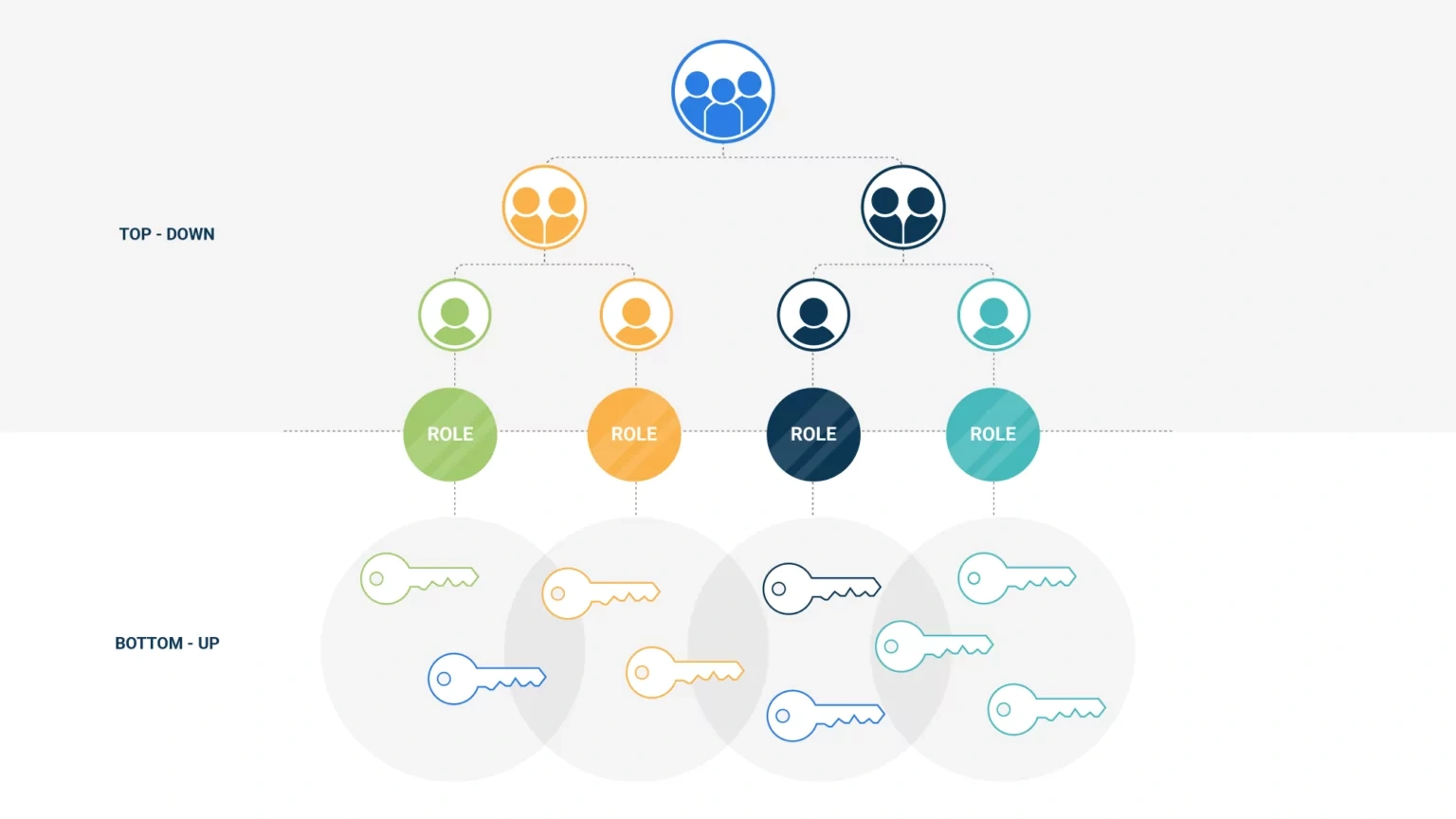
Top-Down
With top-down role engineering, you focus on the existing users and the job functions they perform. You map their activities in detail and identify which applications they use frequently and which they do not. There are several options for conducting this analysis. For example, you can monitor an employee for a day and record which applications they use. You can also interview department managers and ask them to identify which applications their team members need. Also consider involving system owners, who can explain exactly which job functions should never use a specific application.
Regardless of the type of top-down analysis you choose, you determine which applications an employee uses in practice or should use. This lets you revoke authorizations that were granted in error. This is important if you follow a least privilege policy.
Bottom-Up
In addition to a top-down approach, you can also choose a bottom-up analysis. In this case, you do not primarily examine users’ job functions; instead, you look for relationships between granted permissions and specific job functions. If it appears that all employees in the finance department have access to the CRM and order systems, this pattern may indicate that this function always requires access to these systems.
Various tools are available to help you conduct a bottom-up analysis. A key consideration is the quality of your data. The cleaner your data, the more accurate a bottom-up analysis will be. The reverse is also true. Data quality issues in authorizations can lead to incorrect conclusions and degrade the quality of your bottom-up analysis.
Role Mining
Another interesting option is role mining, a method that combines the best of top-down and bottom-up role engineering. The process consists of several steps:
Inventory the existing roles.
Map existing permission groups.
Design your RBAC concept.
Evaluate the concept with stakeholders such as department managers.
Create the first baseline version of the role model based on the results of the steps above.
Role-Based Access Control with HelloID
HelloID is an IAM solution that significantly helps with RBAC. HelloID acts as a broker between your source system (e.g., an HR system) and target systems (e.g., Active Directory (AD), Azure AD, or Google Workspace).
HelloID provides extensive support for both RBAC and ABAC. This gives you the best of both worlds. In HelloID, the role mining process includes the following steps:
Inventory the roles.
Map existing permission groups.
Design an RBAC concept.
Evaluate the concept with stakeholders, including department managers.
These steps produce a first baseline version of the role model that you can apply operationally. You can then expand this model, refresh and update it regularly, and adapt it based on new insights.
It is helpful that HelloID guides you step by step through the role mining process. This allows you to get started with RBAC effortlessly and elevate your organization’s digital security. Curious how HelloID can support this process? Then read our blog post about using smart role mining, where we explain this method in more detail. Want to experience the capabilities firsthand? Book a demo now.
HelloID Software HelloID Whitepaper
Related Articles
- Glossaries
- 9 best practices for identity and access management (IAM)
- RBAC best practices for effective access management
- IAM vs IGA: What Are the Differences?
- Smarter information and access security with AI
- Smart RBAC: prevent role explosion
- Copilot: Protect your data with the right IAM policy
- Navigating the Non-Employee Lifecycle: Ensuring Security and Efficiency
- How do you ensure a good IAM strategy?
- What is a good order for an IAM implementation?