General Data Protection Regulation (GDPR)
The General Data Protection Regulation (GDPR) has been in force across the entire European Union (EU) since May 25, 2018. The GDPR replaces outdated national privacy laws, providing an EU-wide framework that is better equipped to address ongoing digitalization.
In this article, we provide an overview of the GDPR. We first outline what the GDPR defines and why it was created. We then describe the 6 basic principles of the GDPR, who the law is intended for, and how you can better manage and protect personal data.
What is the GDPR?
The GDPR imposes additional responsibilities and obligations on organizations when processing personal data. At the same time, the law grants additional rights to individuals whose data is collected. Processing personal data can cover many activities. It is not only about what an organization does internally with collected personal data. There are also strict rules governing the forwarding, distribution, disclosure, and combination of data. To enforce those rules, national privacy regulators have more options under the new law to ensure compliance and impose fines for violations or data breaches. In the Netherlands, the Dutch Data Protection Authority enforces the GDPR.
What prompted the GDPR law?
There were already laws governing the handling of personal data, but they were quite outdated and not uniform across Europe. The 1995 Data Protection Directive was an EU directive that each country implemented as local privacy laws. In the Netherlands, we used the Personal Data Protection Act until 2018. Each European country had different laws, which made international business, collaboration, and enforcement increasingly difficult. It is unworkable if you operate in multiple countries, each with different rules governing the use of personal data.
The GDPR resolved this and ensures that you have the same obligations and protections across all EU member states. Once you move outside the EU, you must remain careful. EU privacy laws apply in principle to the data of European citizens even outside the EU. However, because the EU is well ahead internationally in privacy legislation, you should not assume your data will always be handled in accordance with the rules in other jurisdictions. For example, at TikTok, a Chinese platform, they do not appear to be very concerned about European privacy guidelines.
Another trigger for the GDPR is rapid digitalization. When the GDPR's predecessors took effect in 1995, the internet was still in its infancy. In 1994, Prime Minister Kok had no idea how to operate a computer, and online we barely went beyond emailing, reading the news, and looking up information. Privacy laws already determined which data could be collected and how, but it was less clear what you were allowed to do with it. As an individual citizen, you had little control over that data.

What Exactly Is Personal Data?
Under the GDPR, personal data is any data that directly or indirectly says something about you. This is common data, such as your name, address, city, and phone numbers, but also photos that show you, your Google search history, and your match results at the tennis club. Some personal data relate directly to you as a person. Other data do not concern you directly, but can be traced back to you, and when combined with other data, say something about you as a person. With your smartphone's IP address, for example, online data can be linked to your device and its associated data.
Under the GDPR, personal data may be processed only for specified purposes. In addition to the above standard personal data, the GDPR distinguishes several other categories of personal data to which special rules apply: special categories of personal data and criminal data.
Special Categories of Personal Data
Special categories of personal data are particularly sensitive. The impact is significant if such data falls into the wrong hands, which is why the GDPR provides additional protections for this data. You should assume that you are not allowed to process this type of data unless there is a statutory exception in the law.
Examples include data revealing a person’s race or ethnic origin, or their political, religious, or philosophical beliefs. Genetic data, biometric data, health information, sexual behavior, or sexual orientation are also special categories of personal data. Union membership is included as well.
Criminal Data
Criminal data includes criminal convictions, offenses, and substantiated suspicions. Certain government organizations, particularly within the Ministry of Justice and Security, may process this data in accordance with strict legal requirements. Otherwise, these data may not be used for any purpose.
In addition to the categories listed, the term sensitive personal data is often used. These are ordinary personal data that are particularly sensitive if disclosed improperly, such as in a data breach. This includes your financial data, location, citizen service number (BSN), and all electronic communications, such as email and chat messages. There are no additional rules under the GDPR, but given their sensitivity, it is advisable to handle them with extra care.

GDPR Principles
The GDPR sets much stricter rules on which data may be collected and for what purposes. We must now inform the individuals involved much better and, in many cases, also request consent. As a citizen, you can withdraw that consent. You also have the right to be forgotten. Under this right to erasure, you may demand that data that does not need to be retained by law be deleted from systems. The GDPR as a whole consists of a substantial text of 99 articles, but the essence can be found in the six principles in Article 5:
Lawfulness, Fairness, and Transparency
Organizations may process personal data only when there is a lawful basis. There are different bases that we will go through in the next section. Organizations must also handle data fairly and transparently. For example, they must clearly inform data subjects of the data they collect and how it is used.
Purpose Limitation
Personal data must be collected for a clearly defined purpose. That purpose may not be silently changed, and you may not repurpose the data without a valid basis. If you ask someone for their address to deliver an order, you may not use that same address to send promotional flyers without a valid basis.
Data Minimization
If there is a specific purpose for collecting data, you may collect only the data that is necessary for that purpose. It is logical for an online shoe store to ask for a customer's shoe size to serve them. However, income, sexual preferences, and family composition are not needed for that purpose.
Accuracy
If an organization collects personal data, it must process it accurately and make reasonable efforts to ensure that all data is accurate.
Storage Limitation
This is also known as retention limitation. You may not retain collected data indefinitely. You may store data only as long as needed for the agreed purpose. After the agreed period, the shoe store must delete your data. A complicating factor is that similar data can have different retention periods depending on the purpose. You must promptly delete a rejected candidate's resume. If someone is hired, then you may retain the resume longer. Storage limitations mean people must review applicable record-retention laws and consider automated data storage.
Integrity and Confidentiality
The principles above address what you may do with data and why. When processing personal data, multiple systems are often used. Organizations must implement technical and organizational measures to protect personal data against unauthorized access and unlawful processing properly. This is not only about preventing external hacking. You must also ensure that employees have access only to the data they need to perform their work.
In addition to complying with the GDPR, it is important to be able to demonstrate compliance upon request, based on your measures. This is called the accountability obligation. The burden of proof lies with your organization.
Lawful Bases Under the GDPR: Why Are You Allowed to Process Someone’s Personal Data?
Every time we use someone’s personal data, it is essentially an intrusion on their privacy. We must do so; otherwise, we could not operate. From the shoe store to your bank, your children’s school, and the municipality, everyone regularly needs personal data to perform their duties. The GDPR describes precisely why certain data may be requested and processed. These are called lawful bases. Each use of personal data must have a basis, and that basis must be clearly recorded. There are six bases, which we briefly explain below:
Consent
In some cases, data may be used without consent. If you were speeding, you would receive a fine by mail, and the CJIB would not first ask whether they may use your address data. Below are several other bases under which your data may be used without consent. In many other cases, consent is required. This ranges from a website that wants to use your data for a newsletter to a sports club that wants to publish a membership list. The GDPR sets strict requirements. Consent must be given freely, and it must be unambiguous which data are collected. The data subject must know who is collecting the data and for what purpose. You must also always be able to verify which consent was given, which data have already been collected, and you may withdraw that consent at any time.
Contractual Necessity
Sometimes, specific data is required to execute an agreement properly. If you buy a new TV, it must be delivered to the correct address. Depending on the payment method, an IBAN may also be required. You may collect that data, although it still helps to be transparent. As soon as you collect more data than strictly necessary to perform your work, explicit consent is required. You may not record family composition during delivery to target your advertising campaigns.
Legal Obligation
Sometimes, authorities may collect data simply because this is required by law. The tax authority requires various personal and financial data to assess your tax and determine your benefits. They do not need to ask you separately, and refusal is not really an option. The same applies to the speeding fine example.
Vital Interests
Sometimes, data is crucial even when consent cannot be obtained. For example, if someone is in an accident and taken to the hospital. Even if the victim is unresponsive, physicians want to be able to examine the person immediately without consent. In that case, necessity overrides other considerations.
Public Interest or Official Authority
For various statutory tasks of public authorities, it may be necessary to collect data. A well-known example is a municipality using surveillance cameras in an entertainment district to enhance public safety. They do not need to ask everyone for individual consent.
Legitimate Interests
The last basis is legitimate interests. An organization may rely on this when information is needed for day-to-day operations. For example, you need employee data for personnel administration. You may collect such data, but you must always carefully assess whether specific data are truly necessary.
Personal Use is Allowed
Sometimes it seems as if nothing is allowed without conditions. People who work with the GDPR also wonder what they can do privately. At home and with friends, you can, fortunately, still use personal data. The birthday calendar in the bathroom can stay. However, if the group of friends grows large enough to constitute an association, the GDPR applies. If your security camera records the public street, then it is a GDPR topic.
Protecting and Managing Personal Data
Where should an organization start when aiming to comply with the GDPR? Use this checklist to access the GDPR Guide, which lets you quickly and easily check in 10 steps how your organization handles privacy:
Step 1: Your Data Processing Activities
First, you will be asked which types of personal data your organization processes. Are these only ordinary personal data, or also special categories of personal data, or, though rarely, criminal data? Depending on the data you have selected, additional privacy rules may apply.
Step 2: The GDPR Bases
You must also clearly indicate which bases you use to collect data. For example, consent, a contract, or a legal obligation. Depending on the basis, there are key considerations. How did you request someone’s consent, and is that information retrievable?
Step 3: Data Protection Officer (DPO)
Do you work in a government institution? Or does your organization collect large-scale data during events? You may then need to appoint a Data Protection Officer (DPO). The DPO ensures that everyone within the organization adheres to the GDPR. For most SMBs that process only ordinary personal data, this is usually not necessary.
Step 4: Data Protection Impact Assessment (DPIA)
A data protection impact assessment (DPIA) is an analysis that anticipates the risks that processing personal data poses to data subjects. For many mid-sized organizations that process ordinary data, this will not be necessary. It is required, for example, if you work with vulnerable individuals, process bulk data, use new technologies such as biometric systems, or make automated decisions based on personal data. If a bank automatically approves or rejects loans based on algorithms that process personal data, a DPIA must be conducted.
Step 5: Privacy by Design and Default
For this check, you must critically review your systems and processes. Verify that your IT systems and procedures are designed to ensure you can always store and process personal data securely, a principle known as privacy by design. Also, ensure systems are configured by default so that data is not readily accessible to everyone, a principle known as privacy by default. No matter how well a system appears to be designed, there is no privacy by default if every user receives an account with a default password and immediate access to all data.
Step 6: Record of Processing Activities
A record of processing activities provides an overview of all types of personal data processed within the organization. Unless you are a very small organization that collects data only sporadically, you should create such a record. It is also useful because you need to have that information readily available anyway.
Step 7: Security
Regardless of what you are allowed to do with data, the data must always be properly secured. This is a challenge when we know that people’s data typically end up in hundreds to thousands of files. In this step, you are asked to verify whether security is adequate. This goes beyond privacy by design and default. It concerns the full business operation, including technical systems and processes. The biggest security risk is usually people. A strong password is excellent, but if it's posted on a monitor with a sticky note, there is still work to do.
Step 8: Data Processing Agreements
The guide is intended for controllers. These are all companies, government agencies, foundations, and even small sole proprietors that process personal data. They may also have their data processed by a third party, known as a processor. For example, a marketing agency to which you send customer data to run a campaign. As the client, you remain responsible.
For example, last year, NS had to notify 780,000 customers that their data had been leaked by its advertising agency. No one wants to be responsible for such a data breach, so you must always conclude a data processing agreement with your processor(s). This records mutual agreements and responsibilities. You make concrete agreements about security, for example.
Step 9: Duty to Inform
Depending on the data you collect and the lawful basis, you must inform the relevant individuals. This can be done through a privacy statement, for example.
Step 10: Privacy Rights
The last step is to ensure that you not only arrange the processing of someone’s data, but also guarantee that people remain in control of their own information. People may request what data you have stored about them. They may also withdraw consent or request deletion of the data. You must have the technical measures and processes in place before you start.
How Can Identity and Access Management (IAM) Help Your GDPR Compliance?
How can a properly implemented IAM solution contribute to compliance with the General Data Protection Regulation (GDPR)? The first five of the previously mentioned GDPR principles focus primarily on what you may do with personal data and your obligations during processing. An IAM platform manages user accounts and access rights and, in doing so, processes data such as names, email addresses, and sometimes phone numbers or dates of birth. The same basic principles apply to an IAM platform itself, but for principle 6, the IAM platform plays an extra central role within an organization:
Data processing must be secured appropriately. Extra-strict rules apply to special categories of personal data, such as health data.
The security of personal data and of the processing applications must be optimal. The GDPR does not provide a single standard approach for this. The principle is that you must take appropriate technical and organizational measures. What that means in your case depends on your specific processing activities and the risks you have identified. The Dutch Data Protection Authority (AP) emphasizes the specific importance of digital access security. It also provides several concrete recommendations and guidelines. We have elaborated on these below, including how an IAM system can help. We illustrate this with HelloID, a modern Identity-as-a-Service (IDaaS) platform.
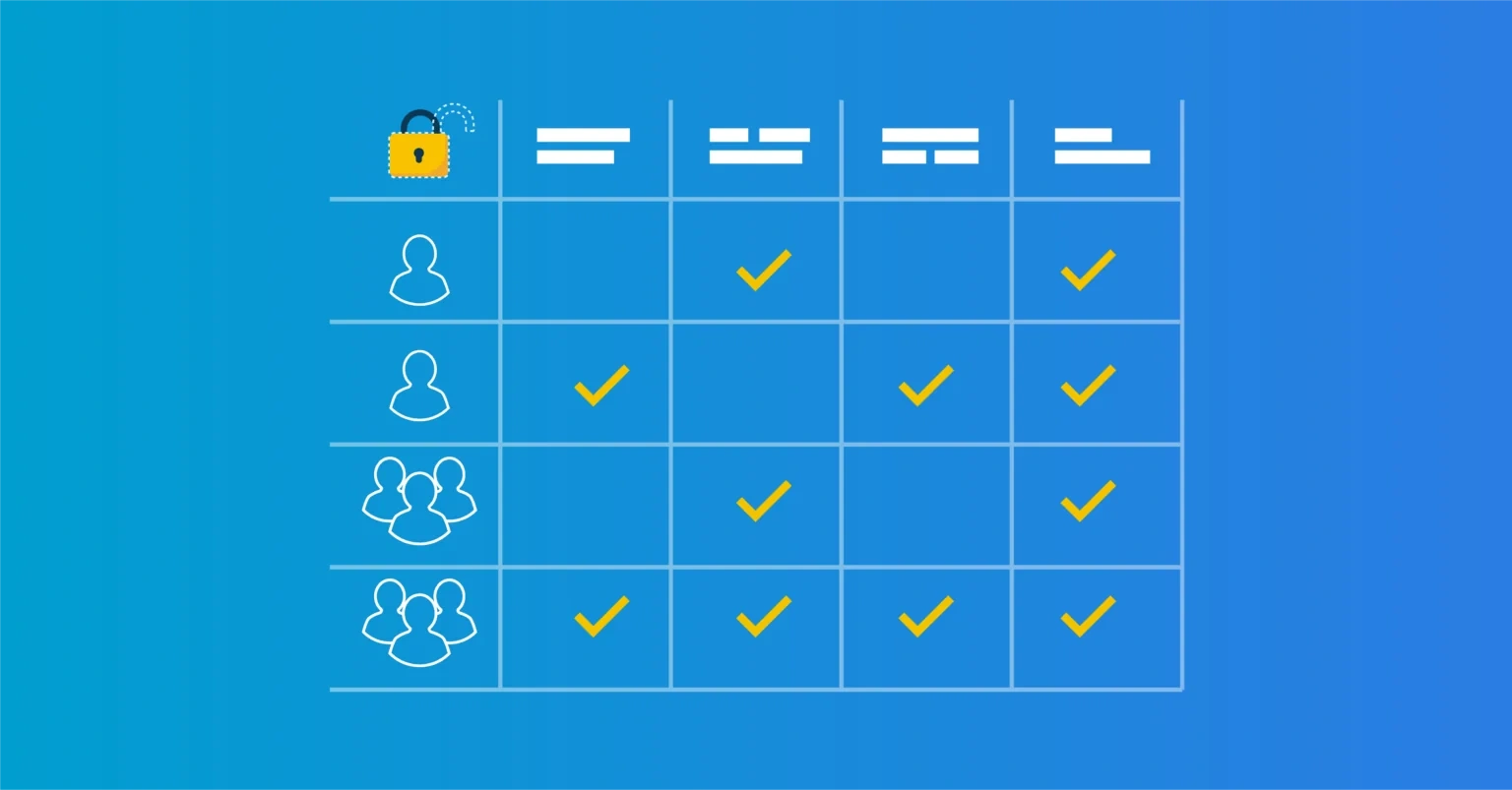
Implement an Authorization Matrix. In such a matrix, all access rights for all systems used must be recorded. It must be clear which information each employee needs to perform their job. The matrix must be sufficiently detailed and kept up to date. Based on this, you can use proper authorization controls to prevent unauthorized access to personal data. If a well-known public figure is staying in your hospital, you want to prevent the entire staff from browsing the medical record.
The 'IAM role' in this recommendation: To implement this GDPR recommendation in a workable way, a state-of-the-art IAM solution is required with Role/Attribute Based Access Control, referred to in this document as RBAC. Only with such a solution can you ensure, in a manageable way, that everyone always has access only to the data and applications they need. You can also guarantee that when someone’s job or role changes, access rights are adjusted immediately. When an employee leaves the organization, this IAM solution ensures access is blocked immediately. In addition, you can automate processes. Temporary accounts are automatically disabled, and before the system activates an account, the user must accept the online privacy rules.
Use multifactor authentication (MFA). It is recommended to enable MFA for all systems with access control. It is also advised for business chat services, such as WhatsApp, and for email applications.
The 'IAM role' in this recommendation: With a modern IAM platform, you can implement MFA effectively and meet this recommendation. A professional IAM solution can also make MFA context aware. For example, you can enforce MFA when accessing sensitive personal data from outside the office or at unusual times. It is important to deploy MFA strategically and prevent 'MFA fatigue'.
Log Access to Systems. It is not only necessary to secure access to systems. It is also necessary to record events in the systems. For example, who performed which processing activities on personal data, and what unauthorized access attempts were made to systems and data. By analyzing such logs, intrusions and attempts can be detected earlier, and, after a security incident, rapid, targeted measures can be taken.
The 'IAM role' in this recommendation: The IAM environment also plays a central role here. With extensive logging functionality, it is always traceable which access attempts were made, when they occurred, and by whom. A good IAM solution is auditable at any time and provides a status overview of all issued accounts, including access rights to applications, data, and other digital resources. It is also traceable who requested an access right and who approved that request.
With the above functions, an IAM system can be a powerful tool for organizations to comply with the GDPR and other privacy laws.
Key Takeaways
The GDPR is a significant improvement over earlier privacy laws. We now protect privacy consistently across Europe, and privacy is much better safeguarded in digital services. There are several points of attention to ensure your organization is compliant with the GDPR:
Ensure that for all personal data you process, you know the purpose of the processing, that it is based on one of the GDPR grounds, and that you have properly documented this. Transparency is essential in the GDPR.
Ensure that you fully inform the people whose data you use. Request consent where needed and ensure both the consent and the stored data are retrievable. Ensure you can answer user questions and delete data upon request.
Use Role-Based Access Control (RBAC) whenever possible. Access rights are automatically linked to a person’s role in the organization. This ensures that only those employees who need personal data for their work can access it. It also ensures that employee accounts are disabled in time to prevent unlawful access. A modern IAM system, such as HelloID, includes RBAC built in.
Implement Multifactor Authentication (MFA) to strengthen system access. For personal data, and especially for special categories of personal data, this adds an extra layer of protection against data breaches.
Ensure your IAM system offers extensive logging and reporting capabilities. In the event of a data breach, you must take action within 72 hours and be able to identify who had access to which data and when specific data were accessed.
Related Articles
- RBAC best practices for effective access management
- Connector team, specialists in smart integrations
- The importance of information security and privacy in education
- IAM increasingly important in education
- How do you ensure a good IAM strategy?
- Data Breach Report: 5 Key Takeaways
- Stopping Privilege Creep in its Tracks
- How Do I Select an IAM Solution
- How Do I Write a Business Case for IAM
- How to Prevent External Access to Key Files