How do you ensure a good IAM strategy?
With a solid Identity and Access Management (IAM) strategy, organizations can achieve their goals faster and more effectively. Everyone has unique objectives, yet we all face similar market conditions, social trends, and technological developments. In this blog, we gather several of these general developments and the impact they have on your digital plans. We then describe how to address them as effectively as possible with strong IAM strategy choices.
Starting point: strategic business trends
Digitalization: In many organizations, data is the most important raw material today. The business is steered with data and business processes are automated as much as possible. This is not only financially driven; we also face a tight labor market. Only by digitizing processes do we preserve enough talent for the roles within organizations where people are indispensable to keep the organization running and make a difference.
Intuitive and hybrid collaboration: Automation and digitalization require user-friendly and intuitive solutions. Employees must be able to work seamlessly from different locations, use various devices, and stay in online contact with colleagues, contractors, customers, and partners. Everyone must be able to collaborate and share data anytime and anywhere.
Focus on core activities: Organizations continuously consider what they must or want to do themselves, and what is better outsourced. Our business models become more refined, with increasing integrations to business processes, applications, and data sources at suppliers, partners, customers, and government entities. At the same time, we outsource our own IT processes and migrate them to the cloud.
Agile operations: Working in an agile manner is more than an IT concept. Organizations as a whole must respond more quickly to new social developments, market trends, and technological innovations. This means we are not only more interconnected with other companies and organizations, but that these relationships and dependencies also change more frequently and faster.
Security and privacy: Continued digitalization increases the vulnerability of organizations and individuals. A hacked server can cause more damage than a facility fire and misuse of personal data can lead to personal harm, devastate our reputation, and result in significant claims and fines. Information security and privacy are boardroom topics.
Transparency and accountability: "As long as nothing goes wrong, we are doing well" is no longer a tenable philosophy. One must be compliant with laws and regulations, but also have the transparency to demonstrate that at any time. If issues occur, we must immediately provide insight into how they arose and how they are resolved. Not only to authorities, but also to customers, partners, and other stakeholders.

IAM strategy choices
Identity and Access Management plays an important role in these developments. There is no one size fits all solution for digitalizing organizations, but regardless of the chosen IT solutions IAM must enable seamless access for all users to those systems. Below we outline six important IAM strategy choices that help streamline your digital plans.
IAM strategy choice 1: Stay in control with an agile IAM
Much existing IAM functionality no longer meets requirements or is end-of-life. A modern Identity and Access Management must be automated, be able to connect to an increasing number of systems, and support all processes. At the same time, big bang implementation projects are rarely an option. A future-proof IAM solution must facilitate a growth path in which we first migrate the basic authentication and authorization functions without issues and from there connect source systems, automate the identity lifecycle, and progressively connect more target systems. In parallel, we can also streamline special cases and further account management processes with service automation. Such a growth path is described in the blog What is a good sequence for an IAM implementation?

That growth path should never be set in stone; a modern IAM environment must be agile. You also do not want to depend on external, expensive specialists and long lead times for further rollout and evolution. The IAM solution must be standard at its core, allowing the internal administration team to add and configure additional functions as add-ons. With sufficient flexibility so that no changes are required in surrounding systems.
If we HelloID as an example: For source and target systems we continuously develop new connectors that customers can easily add as an add-on and configure themselves. The Service Automation module makes it easy to automate and fine-tune service processes, while all RBAC settings and other business rules are simple to configure. This allows the organization to direct the further development of the IAM environment without depending on us as the vendor. All required knowledge is available through free training and online documentation.
IAM strategy choice 2: Cloud-native solution
Technology vendors such as Microsoft focus almost entirely on the development of cloud solutions today. In line with this, most organizations are migrating their IT applications to the cloud, and even the government now applies a yes-if policy for cloud services. A cloud-based Identity and Access Management process is therefore the obvious choice for your modernization plans. However, we are not done yet, because there are multiple cloud strategies possible.
You can opt for a managed service approach where you rehost an existing on-premises solution to an Infrastructure-as-a-Service (IaaS) environment. This appears particularly suitable for larger organizations. It allows for significant custom development, although it carries a corresponding price tag.
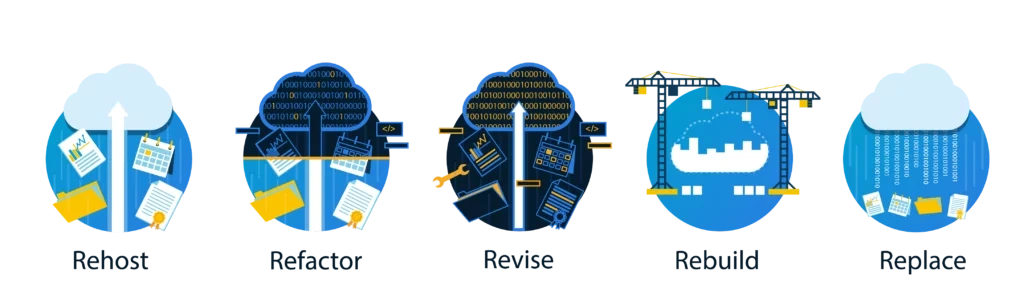
Most organizations will therefore look for a Software-as-a-Service (SaaS) solution. In this model, a service provider offers IAM functionality to multiple customers through a cloud platform. It is important to look under the hood. In some cases, software labeled as SaaS is still the 'old' software delivered via a cloud infrastructure service (IaaS); there has been limited or no investment in rebuilding the software.
A true SaaS solution, such as HelloID, is designed specifically for the cloud, single instance and multi-tenant. This means every customer runs on the exact same codebase and a single instance of the software is used. Only a cloud-native Identity-as-a-Service (IDaaS) environment fully leverages the potential of the cloud.
IAM strategy choice 3: Compliant and auditable
A modern IAM must comply with privacy guidelines such as the GDPR and be compliant with information security standards such as ISO 27001, the BIO and the NEN 7510. That compliance must above all be demonstrable at any time, while in the event of a data breach or another issue a complete audit trail must be available. HelloID, for example, logs all business rule changes, the assessment and processing of permission requests, and other change requests. All access attempts to the infrastructure are also recorded. With standard reports and customer-configurable analytics, you have all input for internal security evaluations, external audits, and formal certification trajectories. In addition to connections to source and target systems, HelloID also offers APIs for integration with other security systems. By connecting an IAM solution to a customer’s SIEM, we can combine the log data with other system logs into a single Single Pane of Glass.

For a cloud-based IAM, not only must the platform comply. The service provider must also be organized for this. Tools4ever, as an IDaaS provider, has a SOC 2 Type II audit report. A Service Organization Controls audit primarily targets service organizations, and a SOC 2 report confirms to customers that the quality of service has been assessed by an independent expert. This assessment includes organizational oversight, vendor management programs, sound software development, internal corporate governance, and risk management processes. The SOC 2 audit is an important addition to the ISO 27001 certification.
IAM strategy choice 4: Automated identity lifecycle management
Issuing and managing user accounts and access rights has traditionally been an IT process. HR teams or team managers submit requests for accounts and entitlements, after which IT support staff manually process the requests in the respective back-office systems. This is a bottleneck in your digitalization; it is inefficient, far from user-friendly, and a source of errors.

A forward-looking IAM environment requires fully business-driven and automated management of users and entitlements. The HR department is in control because it manages all employee data, including agreements on roles, tasks, and obligations. With a direct connection between HR systems and the HelloID environment, the creation and modification of accounts and access rights are fully automated. When employees depart, accounts are automatically terminated. Role Based Access Control is used, in which business rules precisely define which entitlements belong to each role. This prevents undesired accumulation of privileges and enforces the least privilege principle. Everyone receives access to applications and data strictly on a need-to-know basis. With similar connections to other administrative source systems, we can also automatically manage accounts and rights for students, clients, contingent workers, and other user groups.
IAM strategy choice 5: Streamlined (self)service
With automated identity lifecycle management you support the bulk, roughly 80 percent, of your account and access rights management. You also want to streamline the remaining service requests as much as possible under the control of the business; department managers should be able to grant access rights to employees themselves, or users can request them directly online through a portal. HelloID enables this with delegated administration screens that allow managers to perform administrative actions themselves. They can quickly and effectively assess what people need, and the IAM platform then ensures that a change is automatically and correctly processed in the relevant back-office systems. Through the self-service portal end users can also submit requests themselves. An automated process asks the relevant manager or managers for approval online, and it is also possible to grant rights with a limited validity period to prevent undesired accumulation of privileges. Identity and Access Management enables a 'shift left' (moving IT tasks to managers and even end users) in which the business gains more control.

IAM strategy choice 6: Flexible authentication and authorization
Traditionally, an IAM solution supports user authentication and authorization steps. In many organizations this is now provided by Active Directory, Entra ID (formerly Azure AD), Google Workspace, or other Identity Providers. A flexible access management layer remains necessary for well-functioning identity management. For example, to be prepared for migration projects, to easily and quickly onboard new user groups, to allow multiple Identity Providers to work together, and to enable mergers or separations of organizations. A dedicated access management platform is also necessary to support flexible Multi-Factor Authentication and context-aware access services.

Shaping your IAM strategy together?
A good IAM strategy helps you prepare for further digitalization within your organization. This ensures everyone can make optimal use of all digital systems and collaborate seamlessly with colleagues, clients, vendors, and partners.
Curious about the possibilities?
