
Smart Role Mining: The Booster for Role-Based Access Control
Role-Based Access Control (RBAC) is a method for organizations to organize and manage user accounts and access rights in a transparent and secure manner. With a clear set of roles and associated permissions, you know, for every employee and at any moment, which baseline permissions they must have.
Even so, many companies hesitate. Building an authorization matrix with business rules, roles, and permissions seems difficult and time-consuming. That is unfortunate, because it is ultimately the only way to future-proof your identity management. More importantly, introducing RBAC is not difficult if you use the right approach and tools. Role mining is central to that. We explain it below.
How Does Role-Based Access Control Work?
In RBAC (Role-Based Access Control) or ABAC (Attribute-Based Access Control), every user within an organization is assigned a clear role, often tied to job function, department, and location. You then need access rights to specific applications and data to perform that role effectively. In RBAC, you define those role-specific permissions as business rules, so everyone with the same role automatically receives the same permissions. If a user’s role changes, the associated permissions are updated automatically.
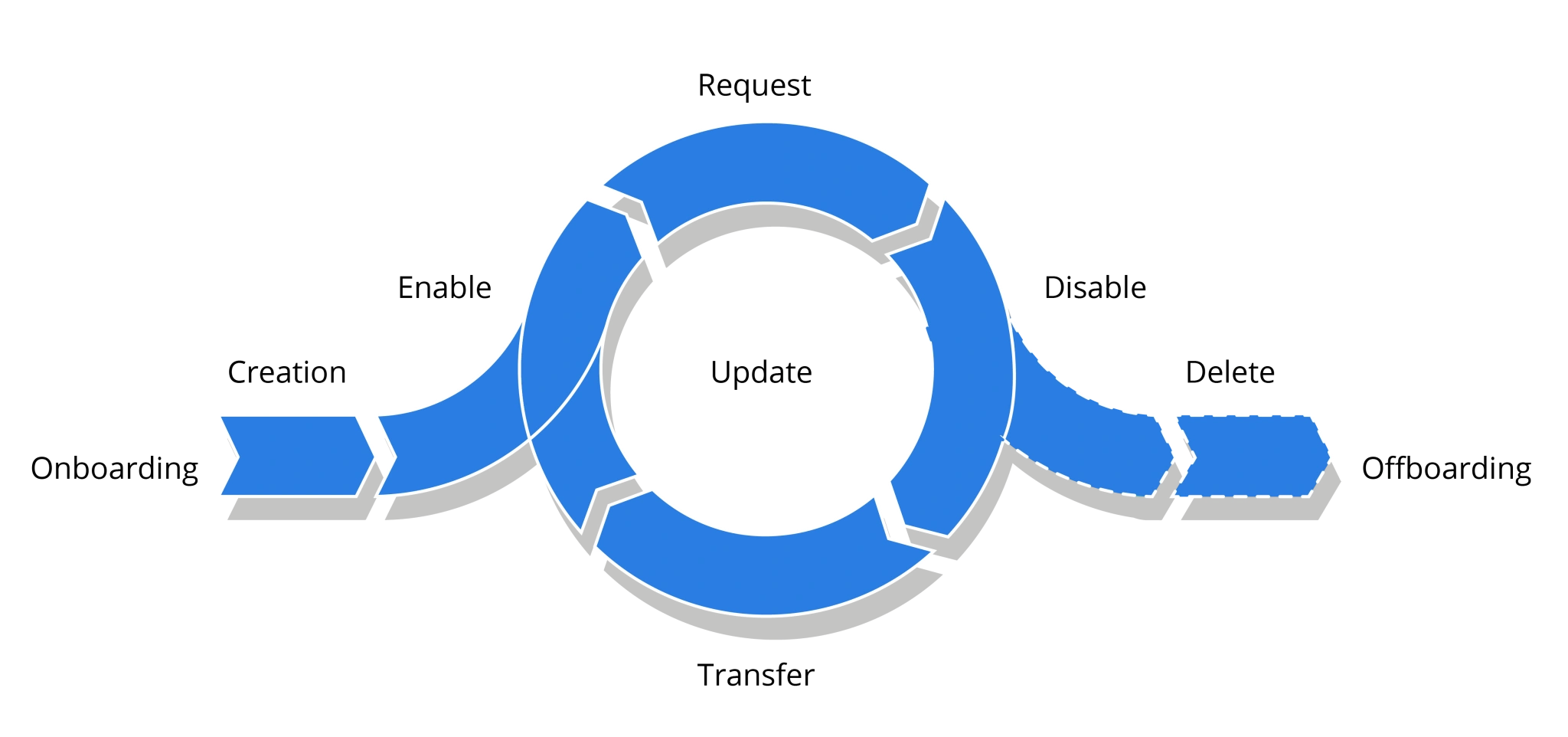
If someone works in the Finance department, in addition to Outlook and Office, they must have access to financial software and data. If that employee later moves into a role on the Sales team, that change is recorded in the HR system and automatically detected by the Identity Management system. Under the RBAC model, it revokes the user's financial permissions and grants access to the CRM system. This is fully automated, so the IT department has minimal follow-up for account and permission management. More importantly, you can be certain that everyone has only the permissions necessary, and nothing more. RBAC forms the foundation of your security and compliance.
Hesitation When Starting With RBAC
It's an ideal model, yet many organizations still hesitate to implement it. Often, organizations still manage user accounts individually, and we regularly see the copy user approach. From such a manual approach, moving to a structured, role-based approach with clearly defined roles and business rules can feel like a major hurdle. How do you build a complex schema from scratch with dozens or hundreds of roles and permissions? How do you involve your department managers and other key stakeholders in that process? How much time does it take to reach consensus? And will your model be outdated by the time you are done? It is an understandable concern, and a slightly different approach can help.
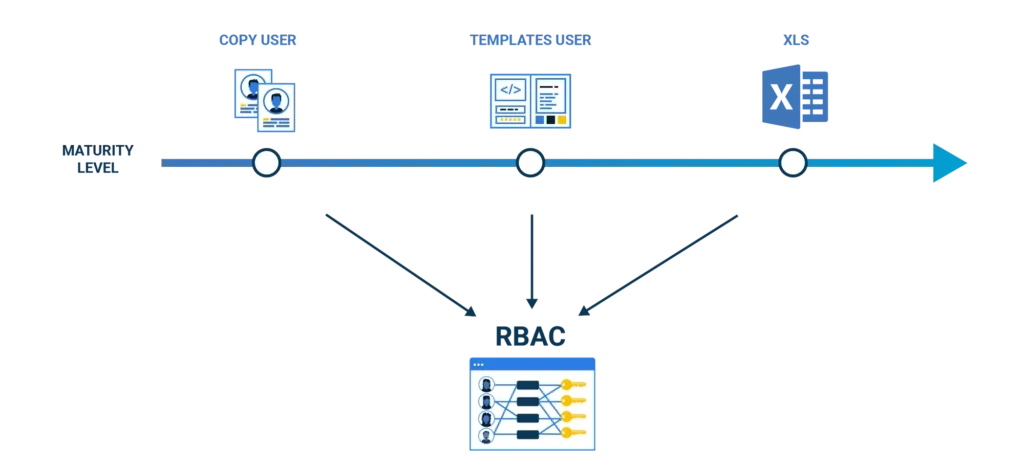
A Manageable RBAC Roadmap Enabled by Role Mining
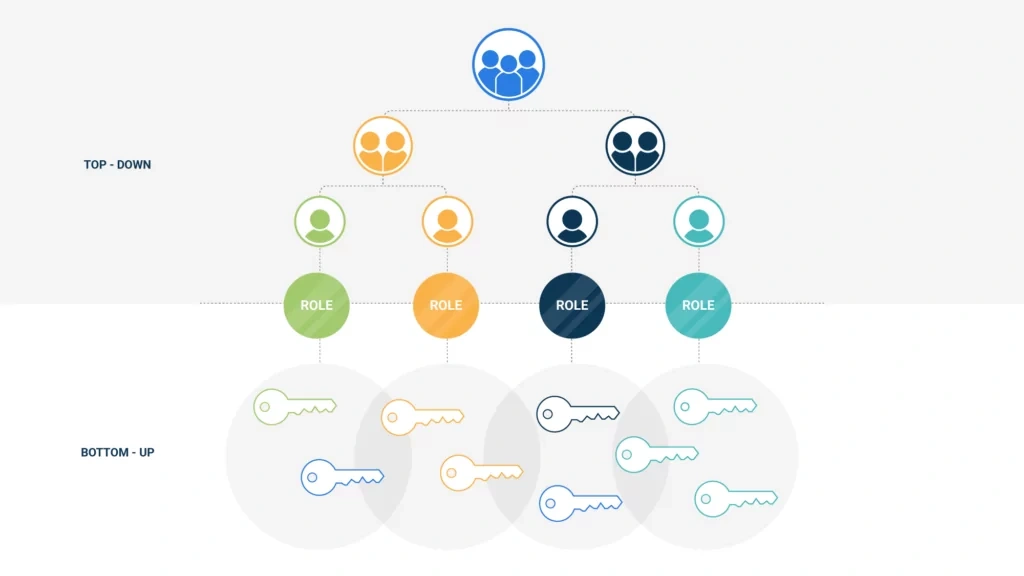
The bulk of the information you need to design an authorization matrix is already available. Even if you have managed accounts and access rights individually up to now, those decisions were still considered. Even when you organize user permissions ad hoc, you typically grant finance staff access to financial systems and sales to the CRM and order system. Permissions may not always have been assigned consistently, and there have undoubtedly been errors and unnecessary permission stacking, but there is already a lot of usable information. How do you extract and analyze that information to develop an initial role matrix? Role mining is an extremely powerful tool for this, combining a top-down and bottom-up approach.
Below are the key steps:
Inventory Existing Roles: We collect, top-down, the different roles that have been recorded in HR.
Inventory Existing Permissions (Groups): We distill, bottom-up, from applications and IT systems, such as an (Azure) Active Directory, the permissions and groups currently assigned.
Design the RBAC Concept: We match the information from steps 1 and 2. We identify authorization patterns from the collected information and incorporate them into an initial concept that defines roles and associated business rules.
Evaluate the Concept with Stakeholders such as Department Managers: Inaccuracies and accumulated noise, for example, due to earlier permission stacking, are identified. Based on this, we refine the concept into a first usable model.
The result is an initial baseline version of the role model that you can apply operationally. From there, the model can be expanded, updated regularly, and adjusted based on new insights.
Role mining is therefore a combination of the right technical tools to extract data from the directory and HR systems, and the analysis and advisory skills to translate that information into an initial role model for your organization. The strength lies in not burdening stakeholders with a blank sheet of paper to build an RBAC model from scratch. You give them a clear starting point with roles and business rules that everyone can comment on. Together, you quickly arrive at your first RBAC implementation.
Keep RBAC Simple and Automate the Exceptions
It is important to recognize that no two people in an organization are the same. Even when people share a similar primary role, there are many exceptions. Someone may be assigned specific tasks or temporarily assigned to a project. People can also, for example, become a works council member or be trained as an emergency response officer. Specific permissions often apply here, and it is a pitfall to include optional permissions in an authorization matrix. To keep your permissions management manageable, you should limit RBAC to birthright permissions, the standard permissions associated with a person’s primary role. An expensive application like Photoshop, or access to a shared project folder, is an example of an optional permission you should manage as an exception. In other words, the goal is not to lock down your RBAC model completely.

These optional permissions are best managed with automated self-service workflows or service automation. Users or their managers can request online access to applications or folders required for their work. Our HelloID Service Automation module ensures that the correct approval steps are followed and that the permissions are then activated in the IT environment. Risky mistakes are prevented in this way.
Automated configuration rules ensure the service catalog stays up to date automatically. A new share, for example, becomes visible in the catalog immediately. With this combination of role-based access control and well-organized service automation, we make managing all user permissions secure, efficient, and controllable.
Learn More About the Tools4ever Role Mining Approach
For organizations that do not yet have a role model, we combine HR and user network data to implement an initial RBAC model through role mining. As described, role mining requires analysis, verification, and consultation in addition to the technical work to develop such a baseline. Key points include removing existing errors, noise, and permission stacking, and the accumulation of permissions. Our business consultants have extensive experience and will help you, through a clear, well-defined consulting engagement, quickly establish a baseline authorization matrix via role mining.
Schedule a Meeting With a Business Consultant
Not ready to schedule a meeting yet, but want to deepen your RBAC or ABAC knowledge? Or do you want to learn how role mining can help you arrive at a role model quickly and with limited resources? We recently hosted a comprehensive webinar on this topic, which you can watch on demand at your convenience.