Use case
Automating Onboarding, Role Changes, and Offboarding Processes
A complete and streamlined onboarding, transition, and offboarding process through advanced lifecycle management and seamless integrations.

CHALLENGE
The Challenges of Manual User and Access Management
Manual onboarding, role changes, and offboarding processes carry a high risk of errors. Examples include inappropriate access being granted, or accounts remaining active after employees leave. This creates serious security risks and leads to non-compliance with applicable privacy and information security guidelines.
REQUIREMENTS
Capabilities
HOW IT WORKS
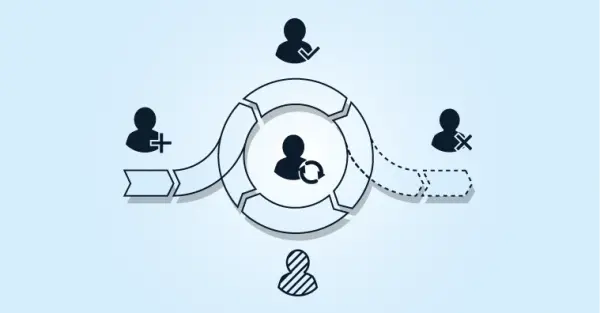
How We Automate the User Lifecycle
Automating the identity lifecycle involves five steps, each of which can be configured using low-code or no-code.

Source Systems: Integrate HelloID with source systems such as HR, SIS, and scheduling systems. Changes to the source data are automatically available in HelloID.
People: Transform person and role data from source systems into a common representation within HelloID using an identity vault.
Business Rules: Define which account types and access rights belong to which roles and under what conditions.
Target Systems: Connect HelloID to on-prem and cloud applications. This can occur incrementally per application.
Reporting and Auditing: Configure standard and customer-specific reports and monitoring functions for analysis and audits.
FAQ
Frequently Asked Questions
Speak with an expert