
SCIM (System for Cross-domain Identity Management)
What is SCIM?
SCIM (System for Cross-Domain Identity Management) is an open standard for the automated management of user accounts in cloud applications and services. Using a SCIM interface, systems can exchange, synchronize, and manage account data, including a person's name, email address, phone numbers, and other user attributes.
Why SCIM?
The need for this SCIM standard arose as account management in cloud environments became more complex. Organizations often have hundreds or thousands of users who use a wide range of applications and data shares. That makes management increasingly complicated. You need an advanced Identity and Access Management (IAM) system that tracks, for each user, which accounts and access rights are required to perform their job.
Example: Is Karen starting as a sales manager in the sales department? Then you want the IAM system to automatically ensure that, during onboarding, she receives, in addition to a basic Microsoft 365 account, accounts for the CRM, quoting applications, and planning software. You also want to grant her access to the data for her specific customers. If, over time, she works with different customers or transfers to a different role in the company, you want her account settings and access rights to be adjusted automatically. An IAM platform provides this.
That means an IAM platform must integrate with all target systems to create accounts, assign permissions, and modify data as needed. To avoid developing a separate connector for each target system, the SCIM standard exists. With SCIM, you have a provisioning API for your account data. You can use it to easily connect target systems to an IAM platform and automatically exchange all relevant identity data.
The first versions of the SCIM standard were developed around 2010 to 2011, resulting in SCIM 1.0. From that version, SCIM evolved into SCIM 2.0 in 2015, which is used today.
Benefits of SCIM
Thanks to the SCIM standard, you gain numerous advantages when implementing your identity management:
Automation: You can easily connect IT systems to a central IAM platform through a SCIM interface and automate account provisioning and synchronization from there. Fewer manual steps are required, and the risk of errors is reduced.
Consistent Management: With automated management, you can be confident that user data is consistently provided and maintained.
Information Security: By issuing user accounts and access rights from a single platform, management becomes more transparent. This prevents unnecessary accounts and permissions from being issued and improves information security.
Efficiency: As a result, you also prevent the issuance of too many licenses. Automation saves not only manual effort but also licensing costs.
Scalability: Thanks to automation, you can manage more user accounts from a single platform and connect to more target systems. Your identity management is no longer a bottleneck for scaling your organization.
However, note that these advantages primarily stem from centralizing your account and permission management through an advanced IAM platform. The specific benefit of a SCIM API is that you do not have to develop and maintain a separate connector for each target system. At the same time, the standard SCIM interface has a few drawbacks, which we discuss later.
How Does SCIM Technically Work?
The SCIM protocol supports identity management in SaaS and other cloud applications. Users of SCIM software use RESTful APIs to create, update, and delete user accounts and groups, making it easier to integrate IAM systems and target systems. There are predefined Schemas and Resource Types for sending identity data such as a person's name, email address, phone number, and other user attributes. The data is exchanged in JSON, making SCIM a lightweight, easy-to-process protocol from a technical perspective.
Use SCIM with HelloID
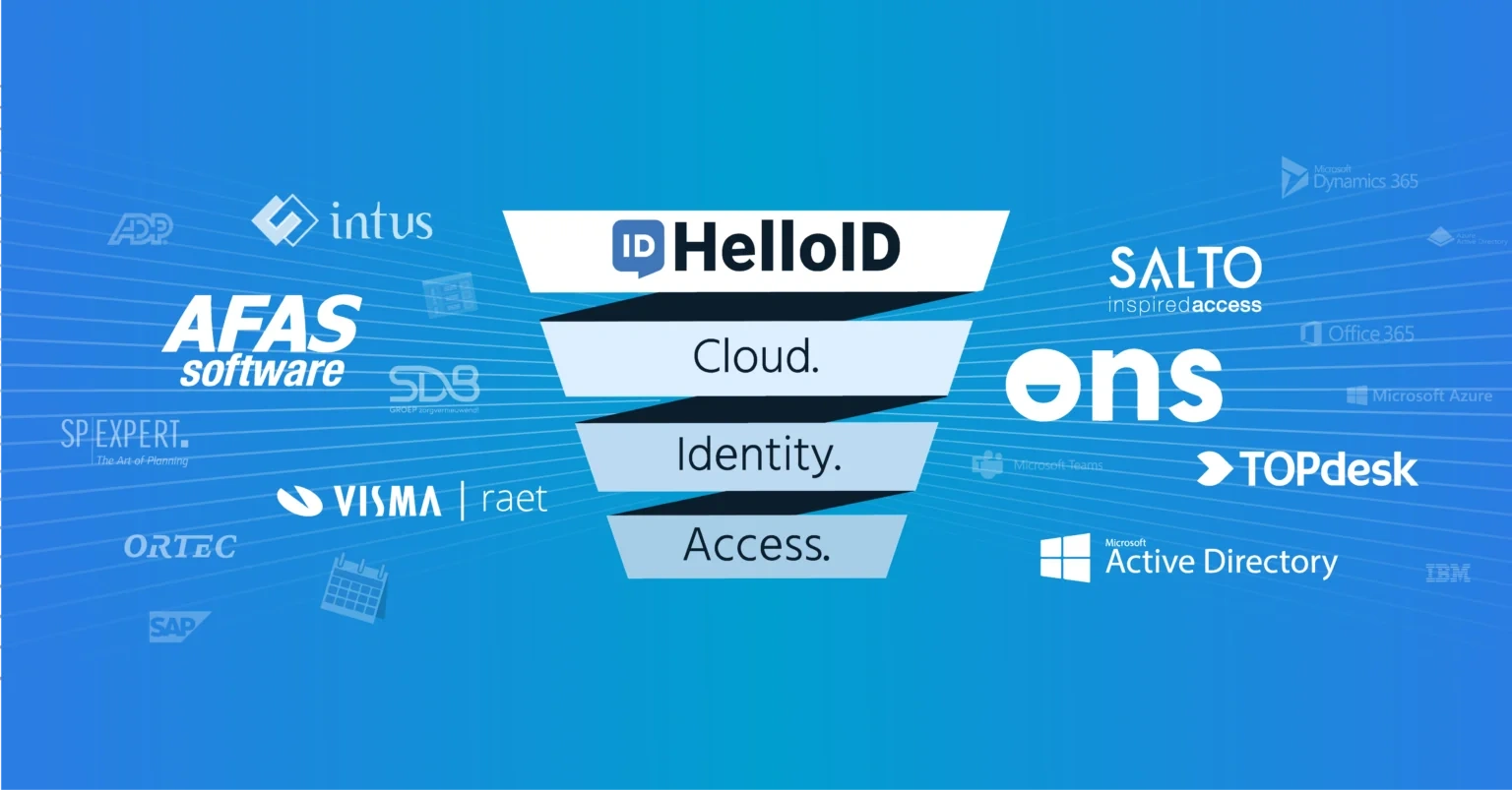
HelloID is a modern cloud-based IAM solution. With the Provisioning and Service Automation modules, customers can ensure that users always receive exactly the accounts and access rights they need for their roles and responsibilities. At the same time, you prevent unnecessary accumulation of access rights and ensure that redundant rights and accounts are cleaned up in a timely manner. For this, HelloID must be connected to source systems, often HR systems, and target systems such as Microsoft 365, a CRM system, or an Electronic Health Record.
HelloID offers an extensive connector catalog that makes it easy to connect hundreds of common applications. When a connector is not yet available, Tools4ever can easily develop it. Every customer can also develop connectors themselves. This can be based on a wide variety of technologies. HelloID supports the SCIM standard for this, but many application integrations have been built using other technologies, such as REST/JSON, SOAP/XML, ODBC, SQL, CSV, and XML.
In any case, many application vendors offer their own API that is not yet based on the SCIM standard. In that case, we use that API for the HelloID connector. It is also true that for many use cases and application vendors, the SCIM standard is actually too limited. For instance, HelloID provisioning functionality effectively offers a superset of the existing SCIM capabilities. The SCIM data model enables setting one department and one job title per user. That may be sufficient for simple organizations, but sometimes you want to register multiple assignments or positions for a single user, including the associated accounts and access rights. In HelloID, you can easily support such broader staffing models through business rules, but SCIM provisioning is too limited for that.
That is why Tools4ever chooses a different type of integration for the source and target systems in those cases. Internally within the platform, we do not use the SCIM definition, but we support the SCIM connector for applications where that is relevant and desired. You can find here more about our provisioning functionality.